共计 9218 个字符,预计需要花费 24 分钟才能阅读完成。
Kubernetes Dashboard 是 Kubernetes 集群的基于 Web 的通用 UI。它允许用户管理在群集中运行的应用程序并对其进行故障排除,以及管理群集本身。
| mkdir /opt/dashboard | |
| cd /opt/dashboard | |
| 创建 kubernetes-dashboard.yaml | |
| apiVersion: v1 | |
| kind: ServiceAccount | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| kind: Service | |
| apiVersion: v1 | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| spec: | |
| type: NodePort | |
| ports: | |
| - port: 443 | |
| targetPort: 8443 | |
| nodePort: 31000 | |
| selector: | |
| k8s-app: kubernetes-dashboard | |
| apiVersion: v1 | |
| kind: Secret | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard-certs | |
| namespace: kube-system | |
| type: Opaque | |
| apiVersion: v1 | |
| kind: Secret | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard-csrf | |
| namespace: kube-system | |
| type: Opaque | |
| data: | |
| csrf: "" | |
| apiVersion: v1 | |
| kind: Secret | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard-key-holder | |
| namespace: kube-system | |
| type: Opaque | |
| kind: ConfigMap | |
| apiVersion: v1 | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard-settings | |
| namespace: kube-system | |
| kind: Role | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| rules: | |
| # Allow Dashboard to get, update and delete Dashboard exclusive secrets. | |
| - apiGroups: [""] | |
| resources: ["secrets"] | |
| resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs", "kubernetes-dashboard-csrf"] | |
| verbs: ["get", "update", "delete"] | |
| # Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map. | |
| - apiGroups: [""] | |
| resources: ["configmaps"] | |
| resourceNames: ["kubernetes-dashboard-settings"] | |
| verbs: ["get", "update"] | |
| # Allow Dashboard to get metrics. | |
| - apiGroups: [""] | |
| resources: ["services"] | |
| resourceNames: ["heapster", "dashboard-metrics-scraper"] | |
| verbs: ["proxy"] | |
| - apiGroups: [""] | |
| resources: ["services/proxy"] | |
| resourceNames: ["heapster", "http:heapster:", "https:heapster:", "dashboard-metrics-scraper", "http:dashboard-metrics-scraper"] | |
| verbs: ["get"] | |
| kind: ClusterRole | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard | |
| rules: | |
| # Allow Metrics Scraper to get metrics from the Metrics server | |
| - apiGroups: ["metrics.k8s.io"] | |
| resources: ["pods", "nodes"] | |
| verbs: ["get", "list", "watch"] | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: RoleBinding | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| roleRef: | |
| apiGroup: rbac.authorization.k8s.io | |
| kind: Role | |
| name: kubernetes-dashboard | |
| subjects: | |
| - kind: ServiceAccount | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: ClusterRoleBinding | |
| metadata: | |
| name: kubernetes-dashboard | |
| roleRef: | |
| apiGroup: rbac.authorization.k8s.io | |
| kind: ClusterRole | |
| name: cluster-admin | |
| subjects: | |
| - kind: ServiceAccount | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| kind: Deployment | |
| apiVersion: apps/v1 | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| name: kubernetes-dashboard | |
| namespace: kube-system | |
| spec: | |
| replicas: 1 | |
| revisionHistoryLimit: 10 | |
| selector: | |
| matchLabels: | |
| k8s-app: kubernetes-dashboard | |
| template: | |
| metadata: | |
| labels: | |
| k8s-app: kubernetes-dashboard | |
| spec: | |
| containers: | |
| - name: kubernetes-dashboard | |
| image: kubernetesui/dashboard:v2.0.0 | |
| imagePullPolicy: Always | |
| ports: | |
| - containerPort: 8443 | |
| protocol: TCP | |
| args: | |
| - --auto-generate-certificates | |
| - --namespace=kube-system | |
| # Uncomment the following line to manually specify Kubernetes API server Host | |
| # If not specified, Dashboard will attempt to auto discover the API server and connect | |
| # to it. Uncomment only if the default does not work. | |
| # - --apiserver-host=http://my-address:port | |
| volumeMounts: | |
| - name: kubernetes-dashboard-certs | |
| mountPath: /certs | |
| # Create on-disk volume to store exec logs | |
| - mountPath: /tmp | |
| name: tmp-volume | |
| livenessProbe: | |
| httpGet: | |
| scheme: HTTPS | |
| path: / | |
| port: 8443 | |
| initialDelaySeconds: 30 | |
| timeoutSeconds: 30 | |
| securityContext: | |
| allowPrivilegeEscalation: false | |
| readOnlyRootFilesystem: true | |
| runAsUser: 1001 | |
| runAsGroup: 2001 | |
| volumes: | |
| - name: kubernetes-dashboard-certs | |
| secret: | |
| secretName: kubernetes-dashboard-certs | |
| - name: tmp-volume | |
| emptyDir: {} | |
| serviceAccountName: kubernetes-dashboard | |
| nodeSelector: | |
| "kubernetes.io/os": linux | |
| # Comment the following tolerations if Dashboard must not be deployed on master | |
| tolerations: | |
| - key: node-role.kubernetes.io/master | |
| effect: NoSchedule | |
| kind: Service | |
| apiVersion: v1 | |
| metadata: | |
| labels: | |
| k8s-app: dashboard-metrics-scraper | |
| name: dashboard-metrics-scraper | |
| namespace: kube-system | |
| spec: | |
| ports: | |
| - port: 8000 | |
| targetPort: 8000 | |
| selector: | |
| k8s-app: dashboard-metrics-scraper | |
| kind: Deployment | |
| apiVersion: apps/v1 | |
| metadata: | |
| labels: | |
| k8s-app: dashboard-metrics-scraper | |
| name: dashboard-metrics-scraper | |
| namespace: kube-system | |
| spec: | |
| replicas: 1 | |
| revisionHistoryLimit: 10 | |
| selector: | |
| matchLabels: | |
| k8s-app: dashboard-metrics-scraper | |
| template: | |
| metadata: | |
| labels: | |
| k8s-app: dashboard-metrics-scraper | |
| annotations: | |
| seccomp.security.alpha.kubernetes.io/pod: 'runtime/default' | |
| spec: | |
| containers: | |
| - name: dashboard-metrics-scraper | |
| image: kubernetesui/metrics-scraper:v1.0.4 | |
| ports: | |
| - containerPort: 8000 | |
| protocol: TCP | |
| livenessProbe: | |
| httpGet: | |
| scheme: HTTP | |
| path: / | |
| port: 8000 | |
| initialDelaySeconds: 30 | |
| timeoutSeconds: 30 | |
| volumeMounts: | |
| - mountPath: /tmp | |
| name: tmp-volume | |
| securityContext: | |
| allowPrivilegeEscalation: false | |
| readOnlyRootFilesystem: true | |
| runAsUser: 1001 | |
| runAsGroup: 2001 | |
| serviceAccountName: kubernetes-dashboard | |
| nodeSelector: | |
| "kubernetes.io/os": linux | |
| # Comment the following tolerations if Dashboard must not be deployed on master | |
| tolerations: | |
| - key: node-role.kubernetes.io/master | |
| effect: NoSchedule | |
| volumes: | |
| - name: tmp-volume | |
| emptyDir: {} | |
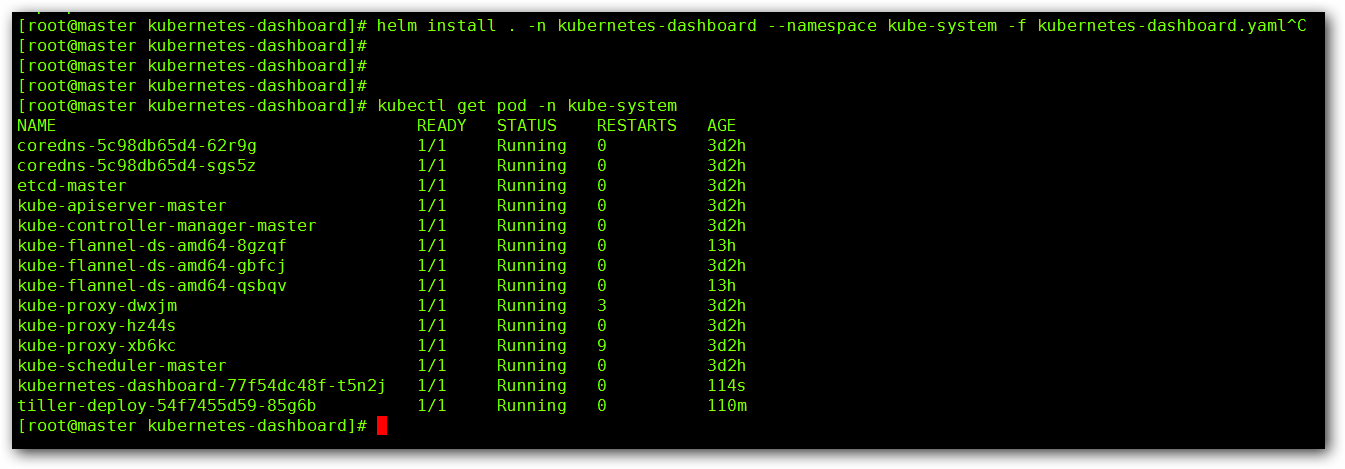
| kubectl apply -f kubernetes-dashboard.yaml | |
| kubectl get pod -n kube-system | |
| kubectl edit svc kubernetes-dashboard -n kube-system |
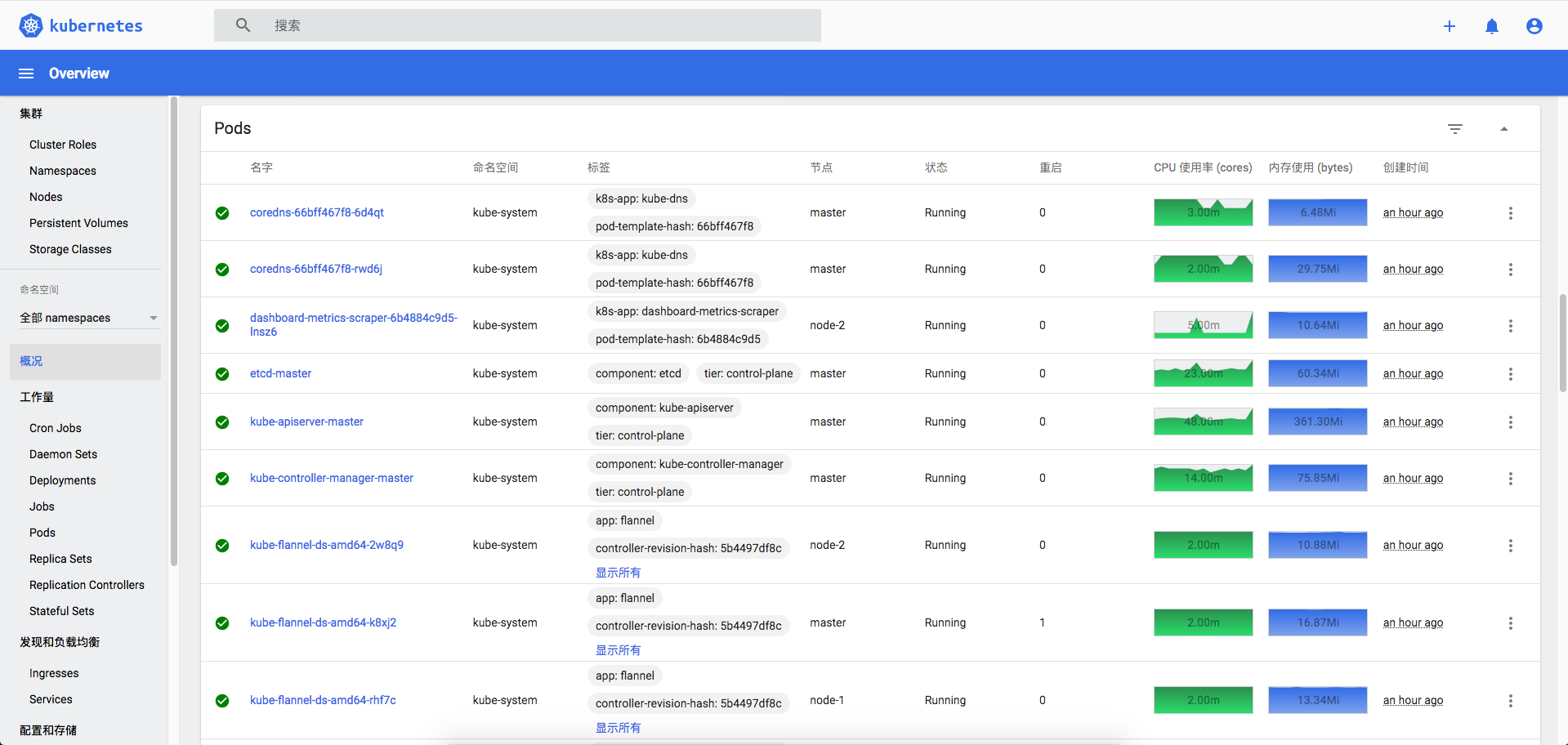
查看资源状态:
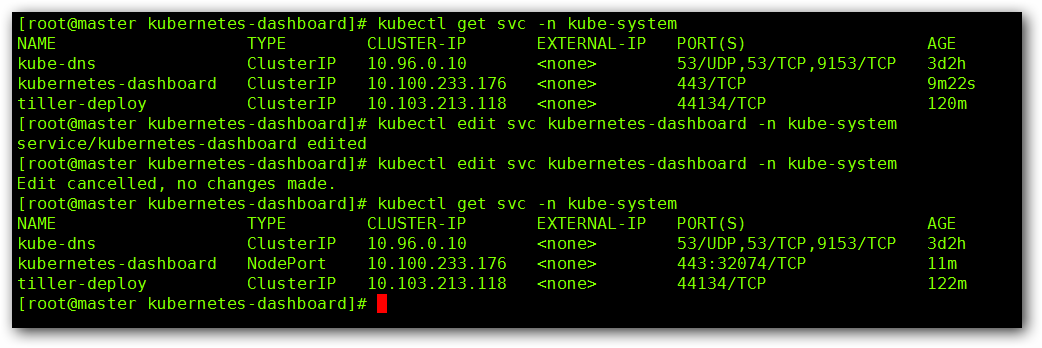
我们可以看到默认的 SVC 类型是 ClusterIP,用命令 kubectl edit svc kubernetes-dashboard -n kube-system 将其修改为 NodePort,看到了暴露的端口号,这个时候我们使用 https://master IP:端口号 进行访问,因为浏览器的问题可能会被拦截,可以使用火狐浏览器进行访问:


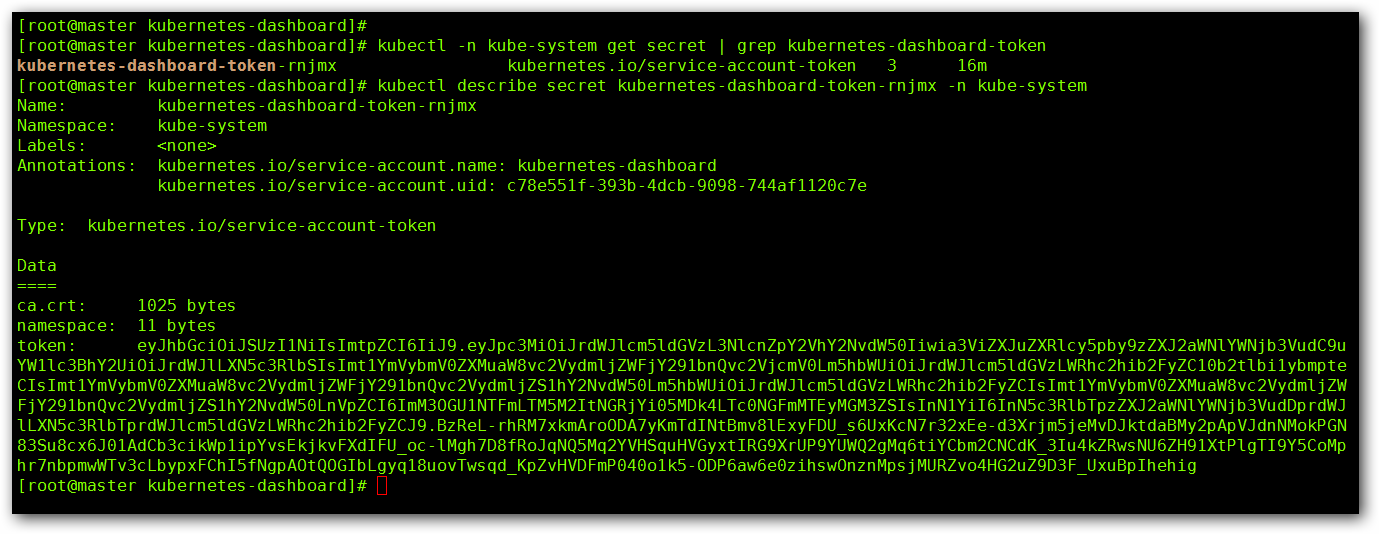
| 通过如下命令就能得到我们的令牌:kubectl -n kube-system get secret | grep kubernetes-dashboard-token | |
| # kubernetes-dashboard-token-rnjmx kubernetes.io/service-account-token 3 32m | |
| kubectl describe secret kubernetes-dashboard-token-rnjmx -n kube-system |
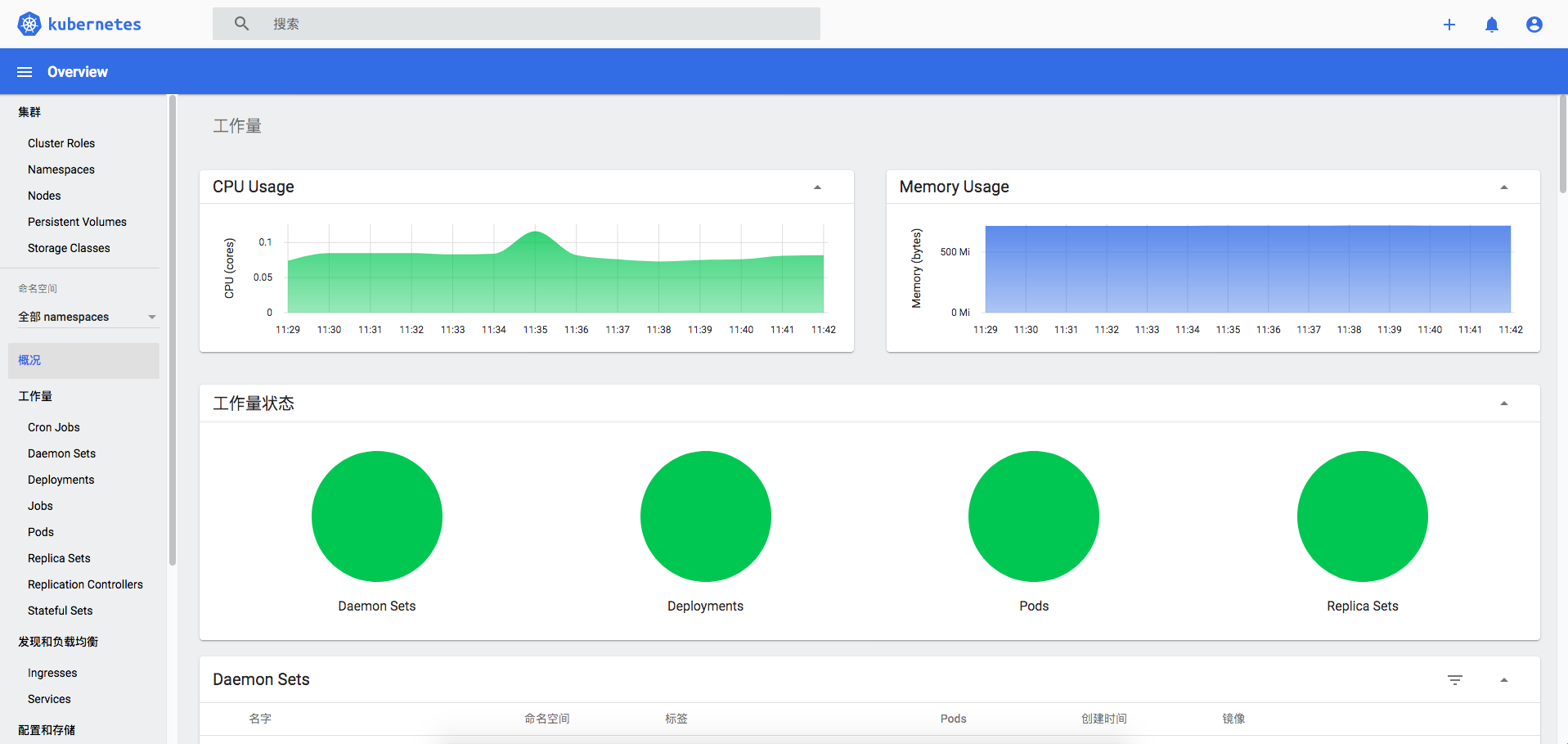
Metrics Server 部署
介绍 Metrics Server 前首先介绍下 Heapster,该工具是用于 Kubernetes 集群监控和性能分析工具,可以收集节点上的指标数据,例如,节点的 CPU、Memory、Network 和 Disk 的 Metric 数据。不过在 Kubernetes V1.11 版本后将被逐渐废弃。而 Metrics Server 正是 Heapster 的代替者。
Metrics Server 是 Kubernetes 集群核心监控数据的聚合器,可以通过 Metrics API 的形式获取 Metrics 数据,不过仅仅是获取指标的最新值,不对旧值进行存储,且不负责将指标转发到第三方目标。Metrics Server 还可以与 Kubectl 工具结合使用,提供 kubectl top 命令来展示集群中的指标数据,接下来我们开始部署 Metrics Server
| cat metrics-server.yaml | |
| ## ServiceAccount | |
| apiVersion: v1 | |
| kind: ServiceAccount | |
| metadata: | |
| name: metrics-server | |
| namespace: kube-system | |
| ## ClusterRole aggregated-metrics-reader | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: ClusterRole | |
| metadata: | |
| name: system:aggregated-metrics-reader | |
| labels: | |
| rbac.authorization.k8s.io/aggregate-to-view: "true" | |
| rbac.authorization.k8s.io/aggregate-to-edit: "true" | |
| rbac.authorization.k8s.io/aggregate-to-admin: "true" | |
| rules: | |
| - apiGroups: ["metrics.k8s.io"] | |
| resources: ["pods","nodes"] | |
| verbs: ["get","list","watch"] | |
| ## ClusterRole metrics-server | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: ClusterRole | |
| metadata: | |
| name: system:metrics-server | |
| rules: | |
| - apiGroups: [""] | |
| resources: ["pods","nodes","nodes/stats","namespaces","configmaps"] | |
| verbs: ["get","list","watch"] | |
| ## ClusterRoleBinding auth-delegator | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: ClusterRoleBinding | |
| metadata: | |
| name: metrics-server:system:auth-delegator | |
| roleRef: | |
| apiGroup: rbac.authorization.k8s.io | |
| kind: ClusterRole | |
| name: system:auth-delegator | |
| subjects: | |
| - kind: ServiceAccount | |
| name: metrics-server | |
| namespace: kube-system | |
| ## RoleBinding metrics-server-auth-reader | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: RoleBinding | |
| metadata: | |
| name: metrics-server-auth-reader | |
| namespace: kube-system | |
| roleRef: | |
| apiGroup: rbac.authorization.k8s.io | |
| kind: Role | |
| name: extension-apiserver-authentication-reader | |
| subjects: | |
| - kind: ServiceAccount | |
| name: metrics-server | |
| namespace: kube-system | |
| ## ClusterRoleBinding system:metrics-server | |
| apiVersion: rbac.authorization.k8s.io/v1 | |
| kind: ClusterRoleBinding | |
| metadata: | |
| name: system:metrics-server | |
| roleRef: | |
| apiGroup: rbac.authorization.k8s.io | |
| kind: ClusterRole | |
| name: system:metrics-server | |
| subjects: | |
| - kind: ServiceAccount | |
| name: metrics-server | |
| namespace: kube-system | |
| ## APIService | |
| apiVersion: apiregistration.k8s.io/v1beta1 | |
| kind: APIService | |
| metadata: | |
| name: v1beta1.metrics.k8s.io | |
| spec: | |
| service: | |
| name: metrics-server | |
| namespace: kube-system | |
| group: metrics.k8s.io | |
| version: v1beta1 | |
| insecureSkipTLSVerify: true | |
| groupPriorityMinimum: 100 | |
| versionPriority: 100 | |
| ## Service | |
| apiVersion: v1 | |
| kind: Service | |
| metadata: | |
| name: metrics-server | |
| namespace: kube-system | |
| labels: | |
| kubernetes.io/name: "Metrics-server" | |
| kubernetes.io/cluster-service: "true" | |
| spec: | |
| selector: | |
| k8s-app: metrics-server | |
| ports: | |
| - port: 443 | |
| targetPort: 4443 | |
| ## Deployment | |
| apiVersion: apps/v1 | |
| kind: Deployment | |
| metadata: | |
| name: metrics-server | |
| namespace: kube-system | |
| labels: | |
| k8s-app: metrics-server | |
| spec: | |
| selector: | |
| matchLabels: | |
| k8s-app: metrics-server | |
| template: | |
| metadata: | |
| name: metrics-server | |
| labels: | |
| k8s-app: metrics-server | |
| spec: | |
| hostNetwork: true | |
| serviceAccountName: metrics-server | |
| containers: | |
| - name: metrics-server | |
| image: registry.aliyuncs.com/google_containers/metrics-server-amd64:v0.3.6 | |
| imagePullPolicy: IfNotPresent | |
| args: | |
| - --cert-dir=/tmp | |
| - --secure-port=4443 | |
| - --kubelet-insecure-tls | |
| - --kubelet-preferred-address-types=InternalDNS,InternalIP,ExternalDNS,ExternalIP,Hostname | |
| ports: | |
| - name: main-port | |
| containerPort: 4443 | |
| protocol: TCP | |
| securityContext: | |
| readOnlyRootFilesystem: true | |
| runAsNonRoot: true | |
| runAsUser: 1000 | |
| resources: | |
| limits: | |
| memory: 1Gi | |
| cpu: 1000m | |
| requests: | |
| memory: 1Gi | |
| cpu: 1000m | |
| volumeMounts: | |
| - name: tmp-dir | |
| mountPath: /tmp | |
| - name: localtime | |
| readOnly: true | |
| mountPath: /etc/localtime | |
| volumes: | |
| - name: tmp-dir | |
| emptyDir: {} | |
| - name: localtime | |
| hostPath: | |
| type: File | |
| path: /etc/localtime | |
| nodeSelector: | |
| kubernetes.io/os: linux | |
| kubernetes.io/arch: "amd64" |
正文完
星哥玩云-微信公众号