共计 4921 个字符,预计需要花费 13 分钟才能阅读完成。
| 导读 | 证书颁发机构 (CA) 是负责颁发数字证书以保证通信安全的实体。它充当证书所有者和依赖证书的一方的受信任的第三方。 |
CA 是公共的,也可以是私有的。公共 CA 通常用于验证网站的身份,私有 CA 用于为客户端到站点 VPN、用户、内部服务器或基础设施内的个人程序和服务生成证书。
在本文中,我们将学习如何在 Ubuntu 20.04 中创建私有证书颁发机构 (CA)。在这里,我们使用 easy-rsa来创建和管理 CA 服务器。
Ubuntu 20.04
EasyRSA 3.0.8
Easy-RSA 是一个命令行工具,极大地促进了证书颁发机构 (CA) 的建立和证书的管理。它会生成一个私钥和公共根证书。
从 github 下载 Easy-RSA 管理工具:
bpang@node02:~$ wget https://github.com/OpenVPN/easy-rsa/releases/download/v3.0.8/EasyRSA-3.0.8.tgz
bpang@node02:~$ tar xvf EasyRSA-3.0.8.tgz
bpang@node02:~$ mv EasyRSA-3.0.8 easy进入 easy 目录,复制一份 vars 变量文件,它用来存放组织信息。
bpang@node02:~/easy$ cp -p vars.example vars编辑 vars 文件
bpang@node02:~/easy$ vim vars将下面几行内容复制到 vars 文件中,修改后面的值为自己想要的。
set_var EASYRSA_REQ_COUNTRY "CN"
set_var EASYRSA_REQ_PROVINCE "BJ"
set_var EASYRSA_REQ_CITY "BJ"
set_var EASYRSA_REQ_ORG "Linuxprobe"
set_var EASYRSA_REQ_EMAIL "test@example.com"
set_var EASYRSA_REQ_OU "COm"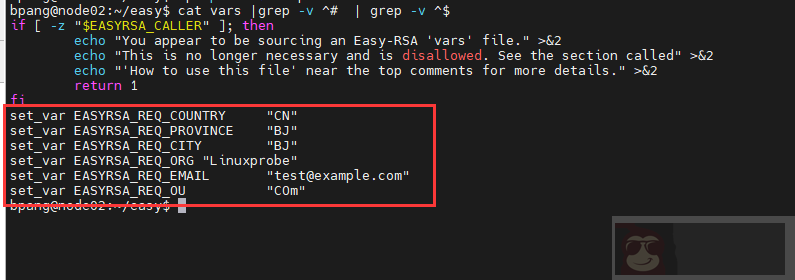
下面来初始化以下目录:
bpang@node02:~/easy$ ./easyrsa init-pki
Note: using Easy-RSA configuration from: /home/bpang/easy/vars
init-pki complete; you may now create a CA or requests.
Your newly created PKI dir is: /home/bpang/easy/pki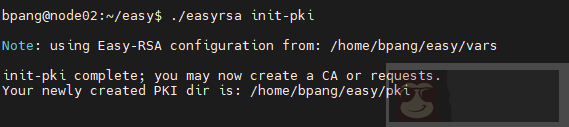
使用下面命令为 CA 服务器生成根私钥对:
bpang@node02:~/easy$ ./easyrsa build-ca nopass
Note: using Easy-RSA configuration from: /home/bpang/easy/vars
Using SSL: openssl OpenSSL 1.1.1f 31 Mar 2020
Generating RSA private key, 2048 bit long modulus (2 primes)
.....................................................................................................................................+++++
..........................................................................................................................+++++
e is 65537 (0x010001)
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Common Name (eg: your user, host, or server name) [Easy-RSA CA]:
CA creation complete and you may now import and sign cert requests.
Your new CA certificate file for publishing is at:
/home/bpang/easy/pki/ca.crt上面命令中的 nopass 不设置密码保护。
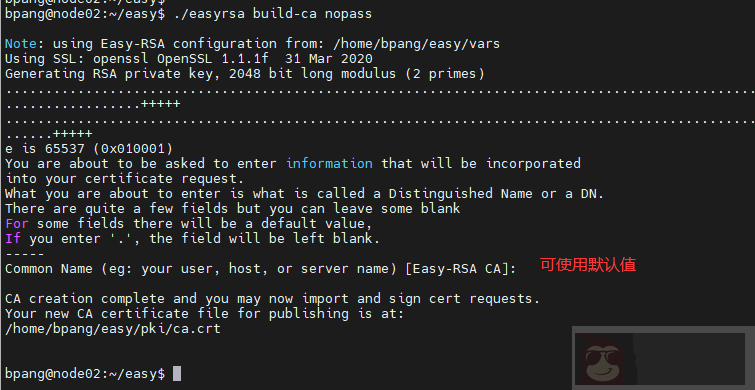
上面的命令已经生成了公私钥了。公钥的位置:/home/bpang/easy/pki/ca.crt,私钥位置:/home/bpang/easy/pki/private/ca.key。Common Name 可以根据需要修改。
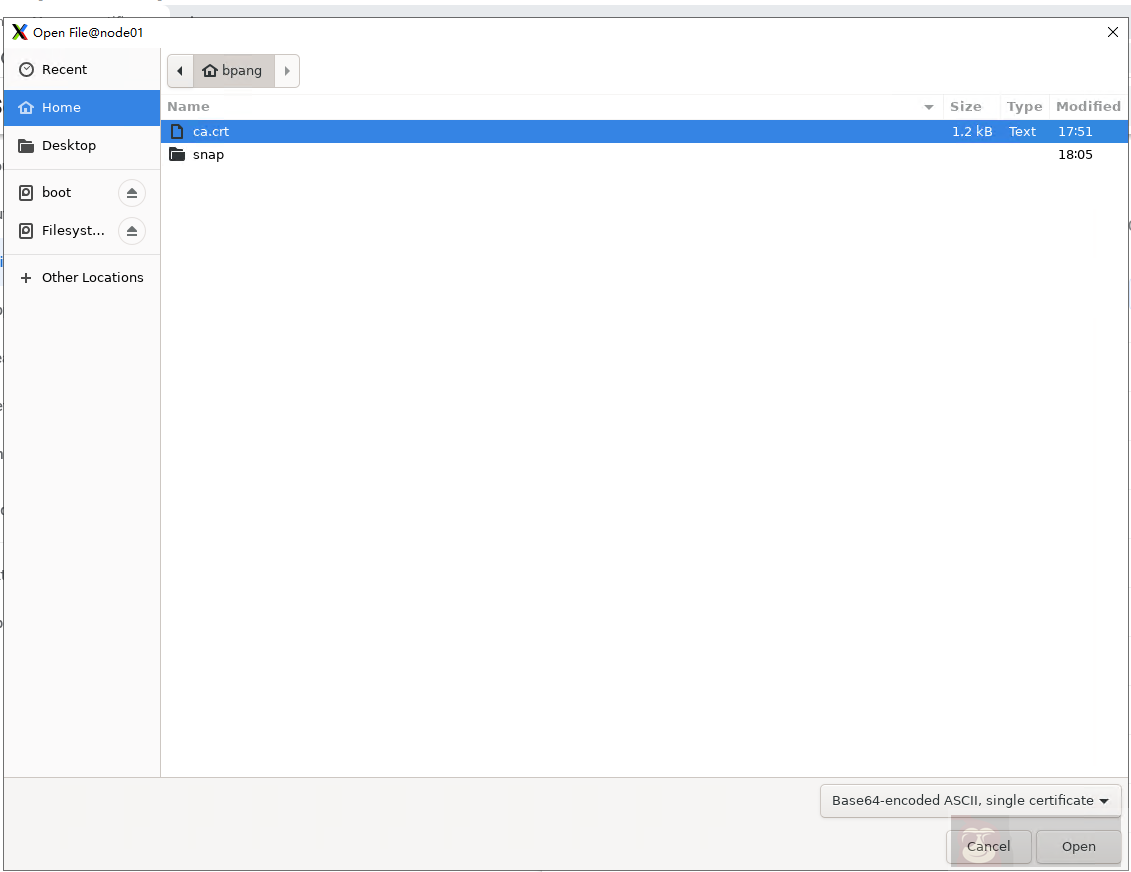
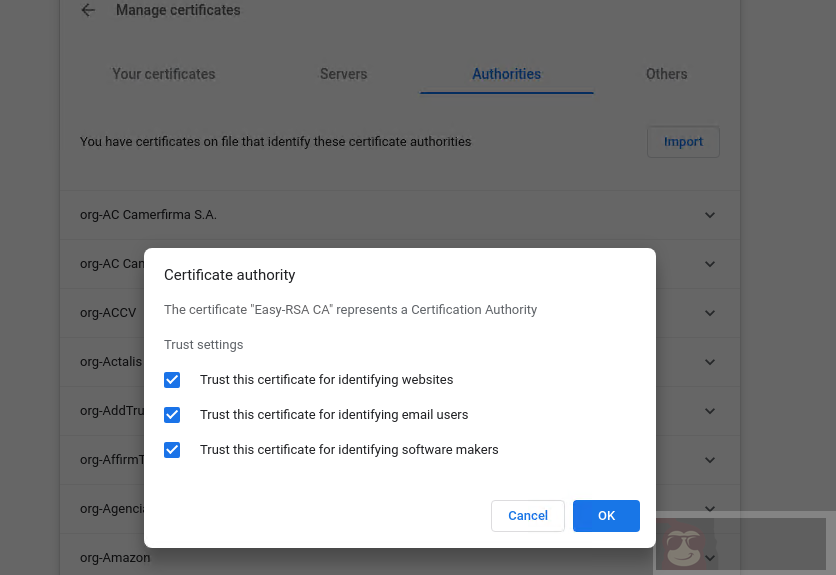
现在我们生成了公共证书,我们需要将它导入到另一台服务器上。
bpang@node02:~/easy/pki$ scp ~/easy/pki/ca.crt root@node01:~然后打开 chrome 浏览器,将 ca.crt 证书导入
Settings – Privacy and security – Security – Manage certificates
我们可以在不同的服务器上创建一些证书签名请求 (CSR),让 CA 证书服务器对这些请求进行签名。
创建一个名为 cert 的目录来保存 CSR 和私钥:
bpang@node02:~$ mkdir cert
bpang@node02:~$ cd cert
bpang@node02:~/cert$使用 openssl 生成私钥:
bpang@node02:~/cert$ openssl genrsa -out server.key 2048
Generating RSA private key, 2048 bit long modulus (2 primes)
.......+++++
....................................+++++
e is 65537 (0x010001)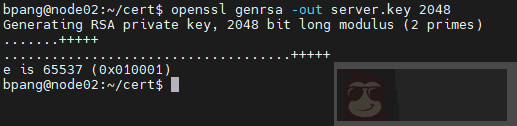
下面用创建的私钥来生成证书请求文件:
bpang@node02:~/cert$ openssl req -new -key server.key -out server.req -subj "/C=CN/ST=BJ/L=BJ/O=Linuxprobe/OU=poc/CN=192.168.56.103/emailAddress=admin@example.com"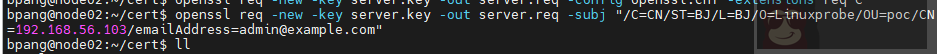
将 csr 证书请求文件复制到 CA 服务器中,用来签名。
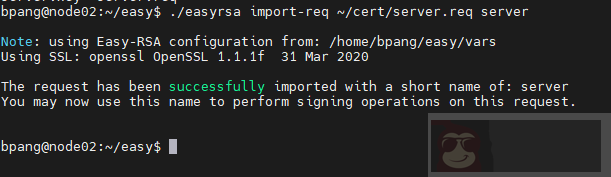
首先使用 easyrsa 工具的 import-req 将请求文件导入:
bpang@node02:~/easy$ ./easyrsa import-req ~/cert/server.req server
Note: using Easy-RSA configuration from: /home/bpang/easy/vars
Using SSL: openssl OpenSSL 1.1.1f 31 Mar 2020
The request has been successfully imported with a short name of: server
You may now use this name to perform signing operations on this request.导入证书请求的语法为:
show-req [cmd-opts]
现在使用以下命令签署 CSR:
bpang@node02:~/easy$ ./easyrsa sign-req server server
Note: using Easy-RSA configuration from: /home/bpang/easy/vars
Using SSL: openssl OpenSSL 1.1.1f 31 Mar 2020
You are about to sign the following certificate.
Please check over the details shown below for accuracy. Note that this request
has not been cryptographically verified. Please be sure it came from a trusted
source or that you have verified the request checksum with the sender.
Request subject, to be signed as a server certificate for 825 days:
subject=
countryName = CN
stateOrProvinceName = BJ
localityName = BJ
organizationName = Linuxprobe
organizationalUnitName = poc
commonName = 192.168.56.103
emailAddress = admin@example.com
Type the word 'yes' to continue, or any other input to abort.
Confirm request details: yes
Using configuration from /home/bpang/easy/pki/easy-rsa-761176.rivirt/tmp.7Wh15B
Check that the request matches the signature
Signature ok
The Subject's Distinguished Name is as follows
countryName :PRINTABLE:'CN'
stateOrProvinceName :ASN.1 12:'BJ'
localityName :ASN.1 12:'BJ'
organizationName :ASN.1 12:'Linuxprobe'
organizationalUnitName:ASN.1 12:'poc'
commonName :ASN.1 12:'192.168.56.103'
emailAddress :IA5STRING:'admin@example.com'
Certificate is to be certified until Aug 13 13:33:36 2024 GMT (825 days)
Write out database with 1 new entries
Data Base Updated
Certificate created at: /home/bpang/easy/pki/issued/server.crt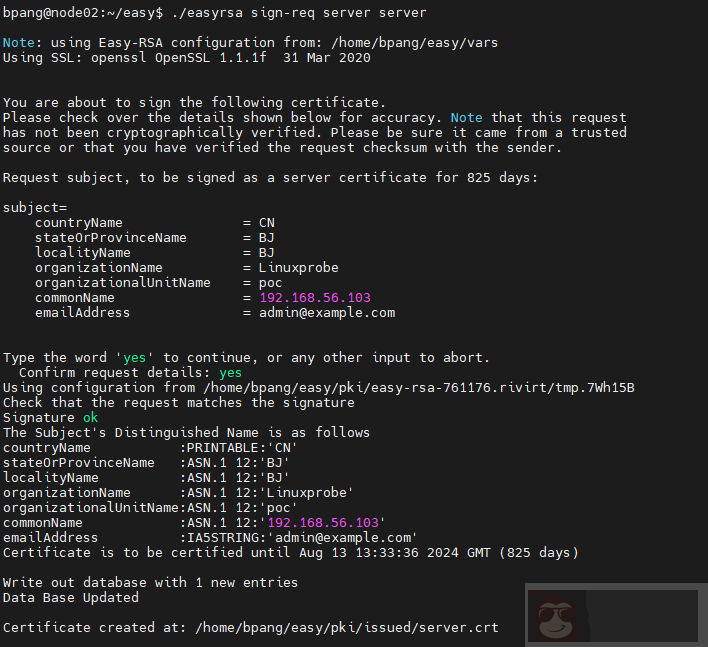
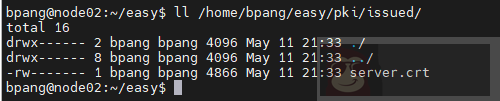
从输出来看证书已经保存到 /home/bpang/easy/pki/issued/server.crt 里面了。验证一下:
下面将证书可秘钥拷贝到 web 服务器中,用来配置 web 的 https:
# 将证书复制到 /etc/ssl/certs
bpang@node02:~$ sudo cp -p easy/pki/issued/server.crt /etc/ssl/certs/
# 将私钥复制到 /etc/ssl/private
bpang@node02:~$ sudo cp -p cert/server.key /etc/ssl/private/修改 apache2 的配置文件,指定 ssl 的证书和私钥文件位置:
bpang@node02:~$ sudo vim /etc/apache2/sites-enabled/default-ssl.conf
SSLCertificateFile /etc/ssl/certs/server.crt
SSLCertificateKeyFile /etc/ssl/private/server.key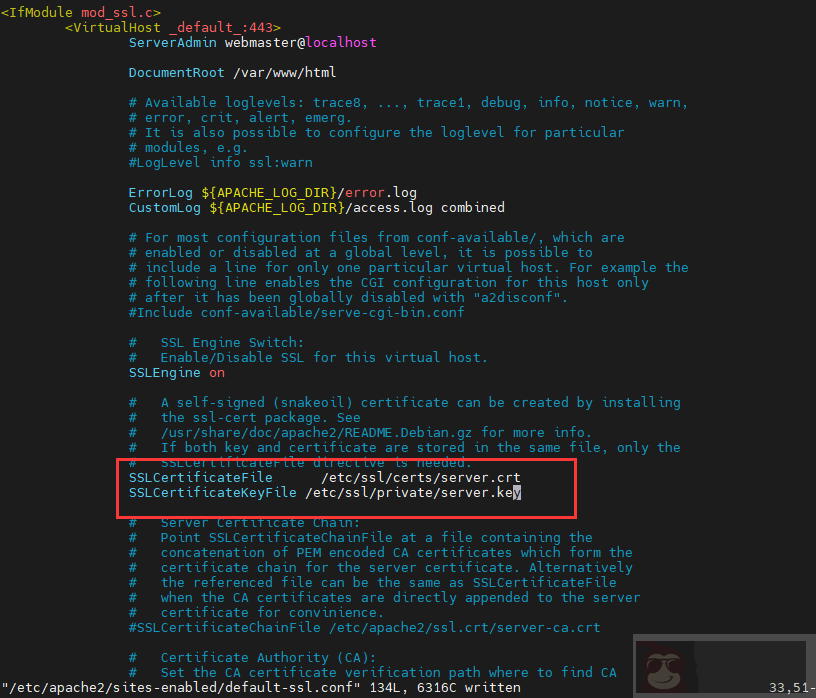
重启 apache。
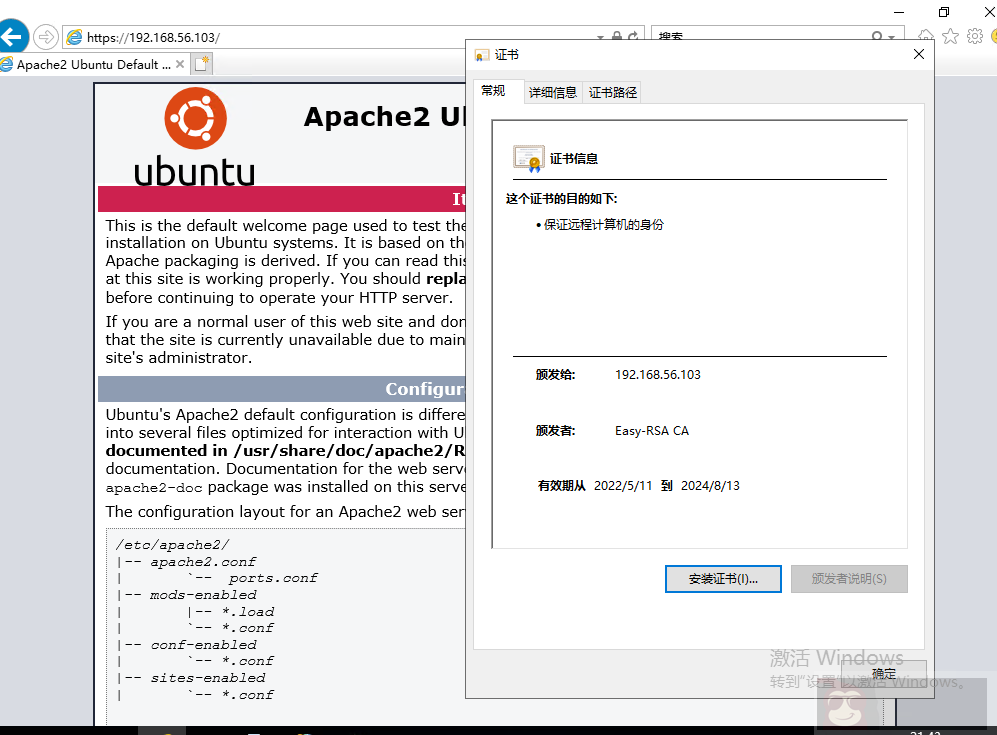
客户端导入根证书之后,访问以下可以看到不再显示 not secure 了。
在本教程中,我们学习了如何在 Ubuntu 20.04 上创建私有证书颁发机构 (CA)。