共计 6458 个字符,预计需要花费 17 分钟才能阅读完成。
本文是一篇关于 Debian 中安装和配置 tripewire 的文章。它是 Linux 环境下基于主机的入侵检测系统(IDS)。tripwire 的高级功能可以检测并报告任何 Linux 中未授权的(文件和目录)的更改。tripewire 安装之后,会先创建一个基本的数据库,tripewire 监控并检测新文件的创建修改和谁修改了它等等。如果修改是合法的,你可以接受修改并更新 tripwire 的数据库。

安装和配置
tripwire 在 Debian VM 中的安装如下。
#apt-get install tripwire
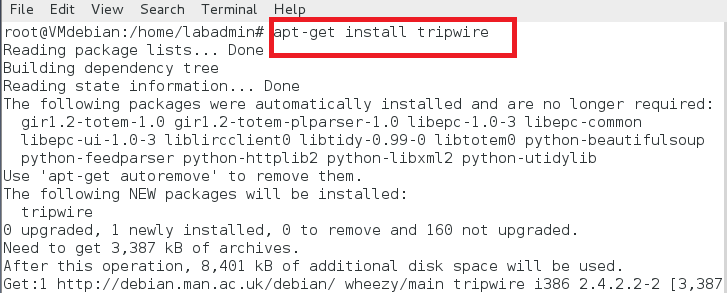
installation
安装中,tripwire 会有下面的配置提示。
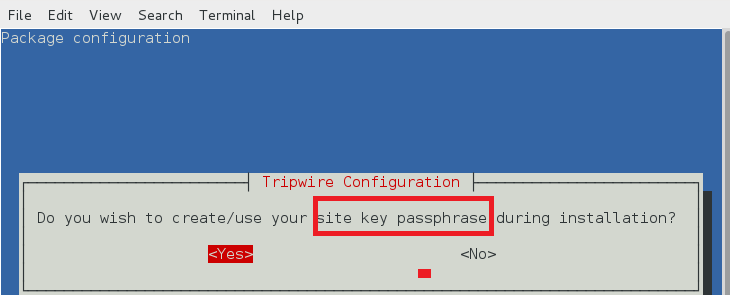
站点密钥创建
tripwire 需要一个站点口令(site passphrase)来加密 tripwire 的配置文件 tw.cfg 和策略文件 tw.pol。tripewire 使用指定的密码加密两个文件。一个 tripewire 实例必须指定站点口令。
site key1
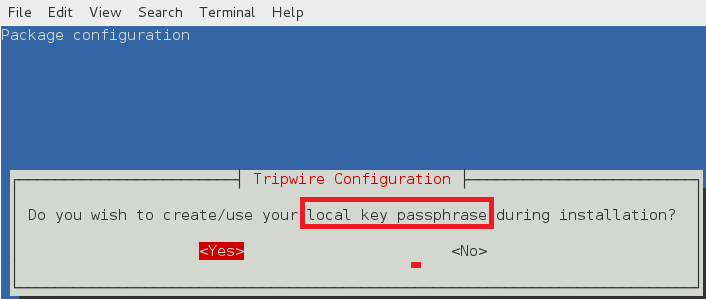
本地密钥口令
本地口令用来保护 tripwire 数据库和报告文件。本地密钥用于阻止非授权的 tripewire 数据库修改。
local key1
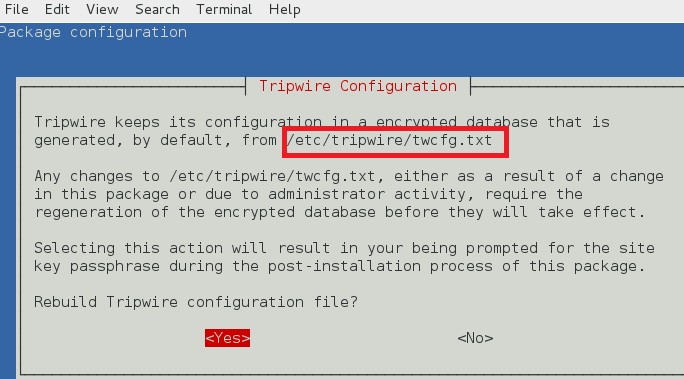
tripwire 配置路径
tripewire 配置存储在 /etc/tripwire/twcfg.txt。它用于生成加密的配置文件 tw.cfg。
configuration file
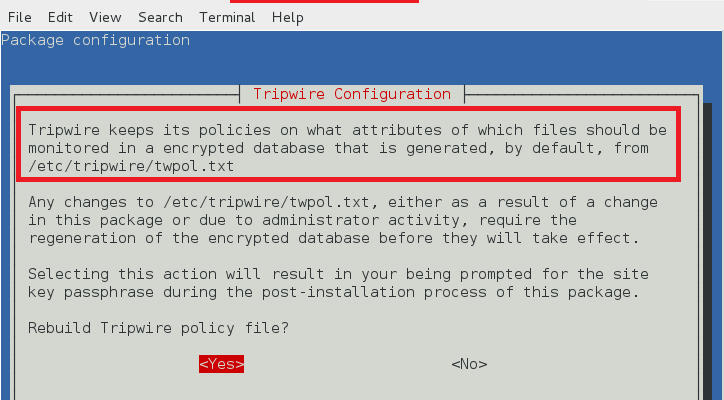
tripwire 策略路径
tripwire 在 /etc/tripwire/twpol.txt 中保存策略文件。它用于生成加密的策略文件 tw.pol。
tripwire policy
安装完成后如下图所示。
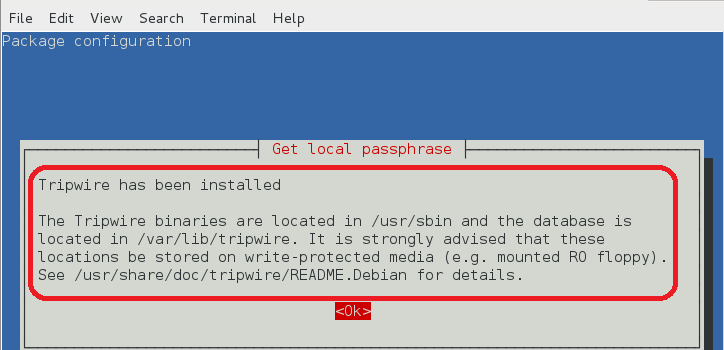
installed tripewire1
tripwire 配置文件 (twcfg.txt)
tripewire 配置文件(twcfg.txt)细节如下图所示。加密策略文件(tw.pol)、站点密钥(site.key)和本地密钥(hostname-local.key)在后面展示。
ROOT =/usr/sbinPOLFILE =/etc/tripwire/tw.polDBFILE =/var/lib/tripwire/$(HOSTNAME).twdREPORTFILE =/var/lib/tripwire/report/$(HOSTNAME)-$(DATE).twrSITEKEYFILE =/etc/tripwire/site.keyLOCALKEYFILE =/etc/tripwire/$(HOSTNAME)-local.keyEDITOR =/usr/bin/editorLATEPROMPTING =falseLOOSEDIRECTORYCHECKING =falseMAILNOVIOLATIONS =trueEMAILREPORTLEVEL =3REPORTLEVEL =3SYSLOGREPORTING =trueMAILMETHOD =SMTPSMTPHOST =localhostSMTPPORT =25TEMPDIRECTORY =/tmp
tripwire 策略配置
在生成基础数据库之前先配置 tripwire 配置。有必要经用一些策略如 /dev、/proc、/root/mail 等。详细的 twpol.txt 策略文件如下所示。
@@section GLOBALTWBIN =/usr/sbin;TWETC =/etc/tripwire;TWVAR =/var/lib/tripwire;##FileSystemDefinitions#@@section FS##First, some variables to make configuration easier#SEC_CRIT = $(IgnoreNone)-SHa;#Critical files that cannot changeSEC_BIN = $(ReadOnly);#Binaries that should not changeSEC_CONFIG = $(Dynamic);#Config files that are changed# infrequently but accessed# oftenSEC_LOG = $(Growing);#Files that grow, but that# should never change ownershipSEC_INVARIANT =+tpug ;#Directories that should never# change permission or ownershipSIG_LOW =33;#Non-critical files that are of# minimal security impactSIG_MED =66;#Non-critical files that are of# significant security impactSIG_HI =100;#Critical files that are# significant points of# vulnerability## tripwire Binaries#(rulename ="tripwire Binaries",severity = $(SIG_HI)){$(TWBIN)/siggen -> $(SEC_BIN);$(TWBIN)/tripwire -> $(SEC_BIN);$(TWBIN)/twadmin -> $(SEC_BIN);$(TWBIN)/twprint -> $(SEC_BIN);}{/boot -> $(SEC_CRIT);/lib/modules -> $(SEC_CRIT);}(rulename ="Boot Scripts",severity = $(SIG_HI)){/etc/init.d -> $(SEC_BIN);#/etc/rc.boot -> $(SEC_BIN);/etc/rcS.d -> $(SEC_BIN);/etc/rc0.d -> $(SEC_BIN);/etc/rc1.d -> $(SEC_BIN);/etc/rc2.d -> $(SEC_BIN);/etc/rc3.d -> $(SEC_BIN);/etc/rc4.d -> $(SEC_BIN);/etc/rc5.d -> $(SEC_BIN);/etc/rc6.d -> $(SEC_BIN);}(rulename ="Root file-system executables",severity = $(SIG_HI)){/bin -> $(SEC_BIN);/sbin -> $(SEC_BIN);}##CriticalLibraries#(rulename ="Root file-system libraries",severity = $(SIG_HI)){/lib -> $(SEC_BIN);}##LoginandPrivilegeRaisingPrograms#(rulename ="Security Control",severity = $(SIG_MED)){/etc/passwd-> $(SEC_CONFIG);/etc/shadow -> $(SEC_CONFIG);}{#/var/lock -> $(SEC_CONFIG);#/var/run -> $(SEC_CONFIG);# daemon PIDs/var/log -> $(SEC_CONFIG);}#These files change the behavior of the root account(rulename ="Root config files",severity =100){/root -> $(SEC_CRIT) ; # Catch all additions to /root#/root/mail -> $(SEC_CONFIG);#/root/Mail-> $(SEC_CONFIG);/root/.xsession-errors -> $(SEC_CONFIG);#/root/.xauth -> $(SEC_CONFIG);#/root/.tcshrc -> $(SEC_CONFIG);#/root/.sawfish -> $(SEC_CONFIG);#/root/.pinerc -> $(SEC_CONFIG);#/root/.mc -> $(SEC_CONFIG);#/root/.gnome_private -> $(SEC_CONFIG);#/root/.gnome-desktop -> $(SEC_CONFIG);#/root/.gnome -> $(SEC_CONFIG);#/root/.esd_auth -> $(SEC_CONFIG);# /root/.elm -> $(SEC_CONFIG);#/root/.cshrc -> $(SEC_CONFIG);#/root/.bashrc -> $(SEC_CONFIG);#/root/.bash_profile -> $(SEC_CONFIG);# /root/.bash_logout -> $(SEC_CONFIG);#/root/.bash_history -> $(SEC_CONFIG);#/root/.amandahosts -> $(SEC_CONFIG);#/root/.addressbook.lu -> $(SEC_CONFIG);#/root/.addressbook -> $(SEC_CONFIG);#/root/.Xresources-> $(SEC_CONFIG);#/root/.Xauthority-> $(SEC_CONFIG)-i ;#ChangesInode number on login/root/.ICEauthority-> $(SEC_CONFIG);}##Critical devices#(rulename ="Devices & Kernel information",severity = $(SIG_HI),){#/dev -> $(Device);#/proc -> $(Device);}
tripwire 报告
tripwire-check 命令检查 twpol.txt 文件并基于此文件生成 tripwire 报告如下。如果 twpol.txt 中有任何错误,tripwire 不会生成报告。
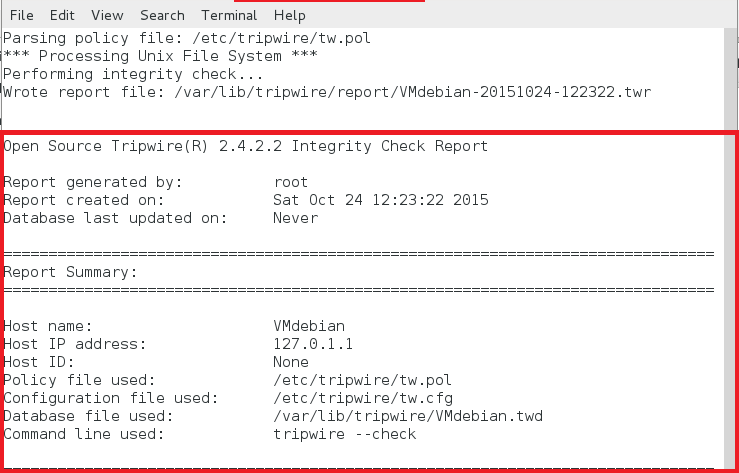
tripwire report
文本形式报告
root@VMdebian:/home/labadmin# tripwire --checkParsing policy file:/etc/tripwire/tw.pol***ProcessingUnixFileSystem***Performing integrity check...Wrote report file:/var/lib/tripwire/report/VMdebian-20151024-122322.twrOpenSource tripwire(R)2.4.2.2IntegrityCheckReportReport generated by: rootReport created on:SatOct2412:23:222015Databaselast updated on:NeverReportSummary:=========================================================Host name:VMdebianHost IP address:127.0.1.1Host ID:NonePolicyfile used:/etc/tripwire/tw.polConfigurationfile used:/etc/tripwire/tw.cfgDatabasefile used:/var/lib/tripwire/VMdebian.twdCommand line used: tripwire --check=========================================================RuleSummary:=========================================================-------------------------------------------------------------------------------Section:UnixFileSystem-------------------------------------------------------------------------------RuleNameSeverityLevelAddedRemovedModified-------------------------------------------Other binaries 66000tripwire Binaries100000Other libraries 66000Rootfile-system executables 100000tripwire DataFiles100000System boot changes 100000(/var/log)Rootfile-system libraries 100000(/lib)Critical system boot files 100000Other configuration files 66000(/etc)BootScripts100000SecurityControl66000Root config files 100000InvariantDirectories66000Total objects scanned:25943Total violations found:0=========================ObjectSummary:================================-------------------------------------------------------------------------------#Section:UnixFileSystem-------------------------------------------------------------------------------No violations.===========================ErrorReport:=====================================NoErrors-------------------------------------------------------------------------------***End of report ***OpenSource tripwire 2.4Portions copyright 2000 tripwire,Inc. tripwire is a registeredtrademark of tripwire,Inc.This software comes with ABSOLUTELY NO WARRANTY;for details use--version.Thisis free software which may be redistributedor modified only under certain conditions; see COPYING for details.All rights reserved.Integrity check complete.
总结
本篇中,我们学习安装配置开源入侵检测软件 tripwire。首先生成基础数据库并通过比较检测出任何改动(文件 / 文件夹)。然而,tripwire 并不是实时监测的 IDS。
via: http://linoxide.com/security/configure-tripwire-ids-debian/
作者:nido 译者:geekpi 校对:wxy
本文由 LCTT 原创编译,Linux 中国 荣誉推出
本文永久更新链接地址 :http://www.linuxidc.com/Linux/2016-04/129806.htm